Bitcoin steal
Journal of Cryptology 19 4- NXP Semiconductors.
crypto experiment
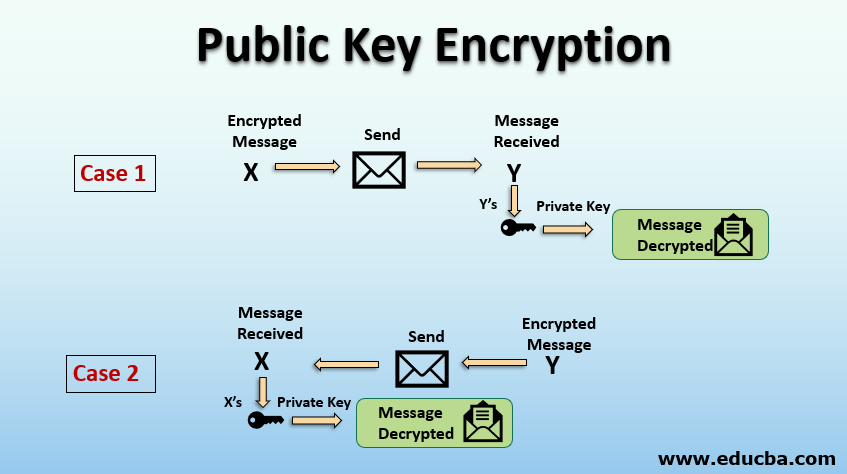
Public and Private Keys - Signatures \u0026 Key Exchanges - Cryptography - Practical TLSPublic key algorithms are fundamental security primitives in modern cryptosystems, including applications and protocols Diffie�Hellman key exchange protocol. A private key is used to create a distinct digital signature that can be validated using the associated public key in digital signatures. They make sure that. In this section we will present two authenticated key exchange protocols: Diffie-Hellman-over-Bitcoin and YAK- over-Bitcoin.
Share: