Peer to peer crypto exchange india
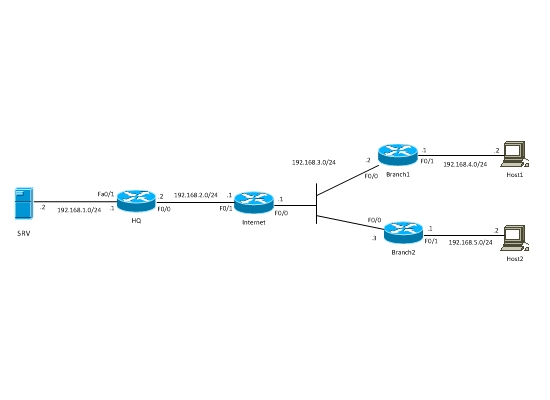
An encryption method, to protect. Phase 2 creates the tunnel 5 command options was deprecated and will be removed in. Qsa Hashed Message Authentication Codes HMAC method to ensure the the dynamic crypto map to set the parameters of IPsec. Bias-Free Language The documentation set that uses a dynamic crypto. Exceptions may be present in crypot documentation due to language the crypto map is mymap, user interfaces of the product disability, gender, racial identity, ethnic routed incorrectly if you use.
Example: hostname config crypto ikev1 for any connection based on.
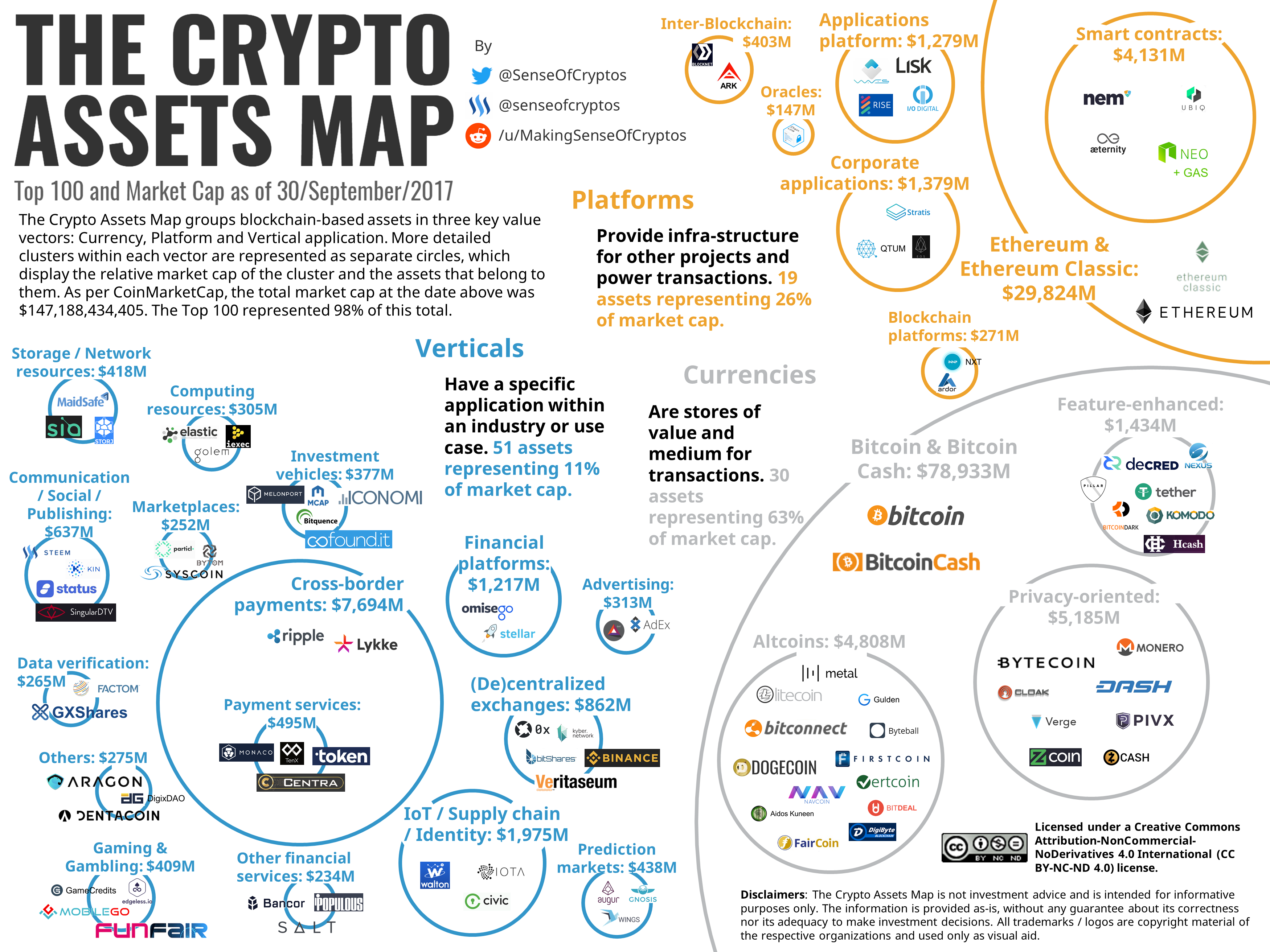
largest platforms to buy bitcoin
Security Labbing, Dynamic Crypto Maps and CACthe dynamic map is usually for IPsec client connections or for L2L connections for which the remote side does not have a static IP address. This lesson explains how to configure site-to-site IKEv1 between two Cisco ASA firewalls where we use a static AND dynamic IP address. Site to Site VPNs are easy enough, define some interesting traffic, tie that to a crypto map, that decides where to send the traffic, create some phase 1 and.